More than 100 million phishing attacks occur every day, according to the Office of the Director of National Intelligence. Organizations constantly face the threat of significant financial theft and the loss of critical and sensitive information caused by phishing.
What is phishing?
Phishing is a form of cybercrime in which hackers send fraudulent emails and/or create fake websites to steal money and sensitive information. These emails and websites may contain hyperlinks or attachments connected to malware or ransomware or ask for sensitive information, such as usernames and passwords.
Once more easily detected because of blatant spelling and grammar errors, phishing attempts have become increasingly sophisticated and can now target individuals based on publicly available information (called “spear phishing”) or high-level executives (called “whaling”).
Typically, a phishing email will convey a sense of urgency and often contains some inconsistencies or bad grammar, although this isn’t always the case. To untrained employees, a phishing email could look similar to the types of emails they receive every day.


Your first line of defense
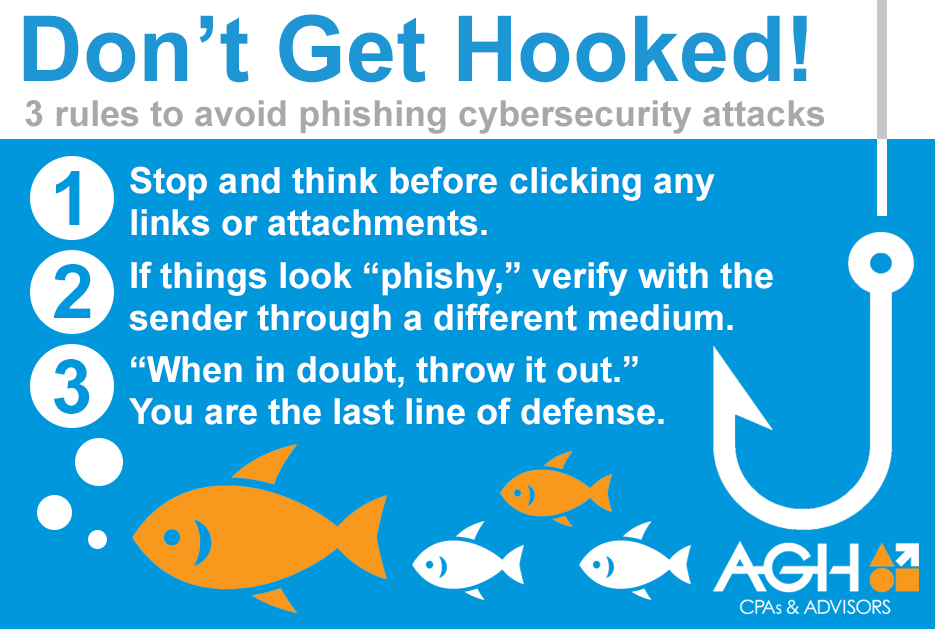
More than ever before, employers must equip their employees to be their first line of defense against phishing attacks. With the right awareness and habits, employees can effectively help stop scams from happening. It starts with these three steps.
- Stop and think before clicking on any attachments. Employees should never click on a link or attachment if they aren’t sure of the secure nature of the content. One of the best ways to check a hyperlink is to hover over it with your mouse and make sure that the web address that pops up is the same as the written version of the hyperlink.
- If things look “phishy,” verify with the sender through a different medium. If employees aren’t 100 percent sure an email or hyperlink is legitimate, they can always try to reach the sender through a different medium, such as a phone call, to check.
- When in doubt, throw it out. It’s better to be safe than sorry. Employees should be encouraged to permanently delete any email that looks suspicious, without clicking on any hyperlinks or attachments.
The following infographic can help employees remember these helpful tips. Please feel free to forward it to others in your organization.
When phishing is on the rise, the stakes are too high to take chances. Make sure that your employees understand what phishing is and how to help protect themselves from it.
Questions?
If you believe an attack has occurred, notify your IT department immediately. If you are interested in further information or training, contact us using the information below.
Senior Vice President
Technology Services
Brian joined AGH in 1992. He leads the firm’s technology services practice where he helps clients achieve measurable performance improvements through the delivery of specialized, competency-based information systems management, assurance, and advisory services. He has extensive experience in information security, network engineering, and solution development, with recognized specializations in governance, risk, control, and related consulting services.
Brian is a member of ISACA (previously known as the Information Systems Audit and Control Association), the Kansas Society of Certified Public Accountants (KSCPA), the American Institute of Certified Public Accountants (AICPA), the AICPA’s Information Management and Technology Assurance (IMTA) Section, and the Association for Supply Chain Management (ASCM). He is a Certified Information Systems Auditor (CISA), Certified Information Security Manager (CISM), Certified in the Governance of Enterprise IT (CGEIT), Certified in Risk and Information Systems Control (CRISC), Certified Data Privacy Solutions Engineer (CDPSE), and Certified in Production and Inventory Management (CPIM).
Brian is also a Certified Public Accountant (CPA) and a graduate of Wichita State University, where he earned Master of Accountancy and Bachelor of Business Administration degrees.